Two Cross-Site-Scripting Vulnerabilities in RocketChat
Introduction
During my work at G Data - Advanced Analytics, Faradax and me found two cross-site-scripting vulnerabilities in RocketChat.
Vulnerabilities
Affected version: < 0.65.0
CVE-2018-13879
The first one is not so critical and during the registration process. During the registration the username field is not filter or escaped. When you create an invalid username, the username will be display unescaped in the following error message.
CVE-2018-13878
The other cross-site-scripting is more serious because it allows running javascript code in the browser of each user that is in the same channel as the attacker.
The setting "Use Real Name" has to be enabled in the settings. Then the attacker goes to their profile changes the display name to a string containing the injection code (e.g. <svg onload=alert(69)>).
To trigger the exploit, the attacker has to use the @ mentioning command in the chat. There the display name is displayed unescaped and the javascript code is run. This way we can exfiltrate the user tokens and steal their session.
It is way more dangerous, if the user uses the offical RocketChat desktop client. The rest is left as an exercise ;).
Disclosure
The vulnerabilites were first disclosed to the offical security e-mail address of RocketChat. I only received a link to Hackerone and they told me to open the issue there. Problem is, the issues were disabled at Hackerone so that was not possible.
I tried it for some more times but noone answered me. Then I created an issue for both vulnerabilities at the GitHub repository and created a pull request.
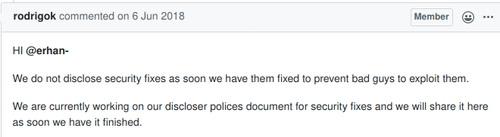
After the release of the new version, nothing about security was mentioned in the release notes. People were not notified for unlogical reasons:
CVE
Following CVEs have been assigned to the vulnerabilites:
Timeline
- 20.04.2018
- Both vulnerabilities sent to security@rocket.chat
- Received link to HackerOne but issues are deactivated there so you can not report there
- 11.05.2018
- Asked the team for an update -> No response
- 17.05.2018
- Still no answer
- Created pull request with fix
- 28.05.2018
- merged and version 0.65.0 release
- No mention of security fix in release notes ...
